Public Records Safety provides actionable resources designed to help counties, system vendors, and local abstractors better understand and manage the risks associated with automated data harvesting.
These materials are built to support real-world implementation—not theory. Whether you are managing a county portal, developing records systems, or working directly with public data, these resources are designed to help you take immediate, practical steps toward protecting your infrastructure.
Everything you need to advocate for public records protection in your county. Download, print, and share.
County public record systems were never designed for automated, large-scale extraction.
What began as digitization for accessibility has unintentionally created an environment where bots and AI systems can access and extract massive volumes of sensitive data—often without detection, control, or accountability.
This creates a growing gap between:
These resources exist to help close that gap.
Without safeguards in place, counties face:
System Performance Issues
Operational Burden
Security Exposure
Public records contain highly sensitive information, including:
When aggregated at scale, this data becomes a powerful tool for:
The issue is no longer theoretical—it is already happening.
Sample robots.txt for County Sites
Copy-paste resources your county IT team or vendor can implement immediately.
Add to your county website's Terms of Use page:
"Automated access to this website, including but not limited to scraping, crawling, data mining, or bulk downloading of records, is prohibited without prior written authorization from [County Name]. Use of bots, scripts, or automated tools to access, search, or download data from this site constitutes a violation of these Terms of Use and may be subject to legal action. This prohibition does not restrict individual, manual searches by members of the public for legitimate purposes."
Most discussions around public records focus on either:
Public Records Safety focuses on the operational middle ground:
This is not about shutting systems down—it’s about making them sustainable.
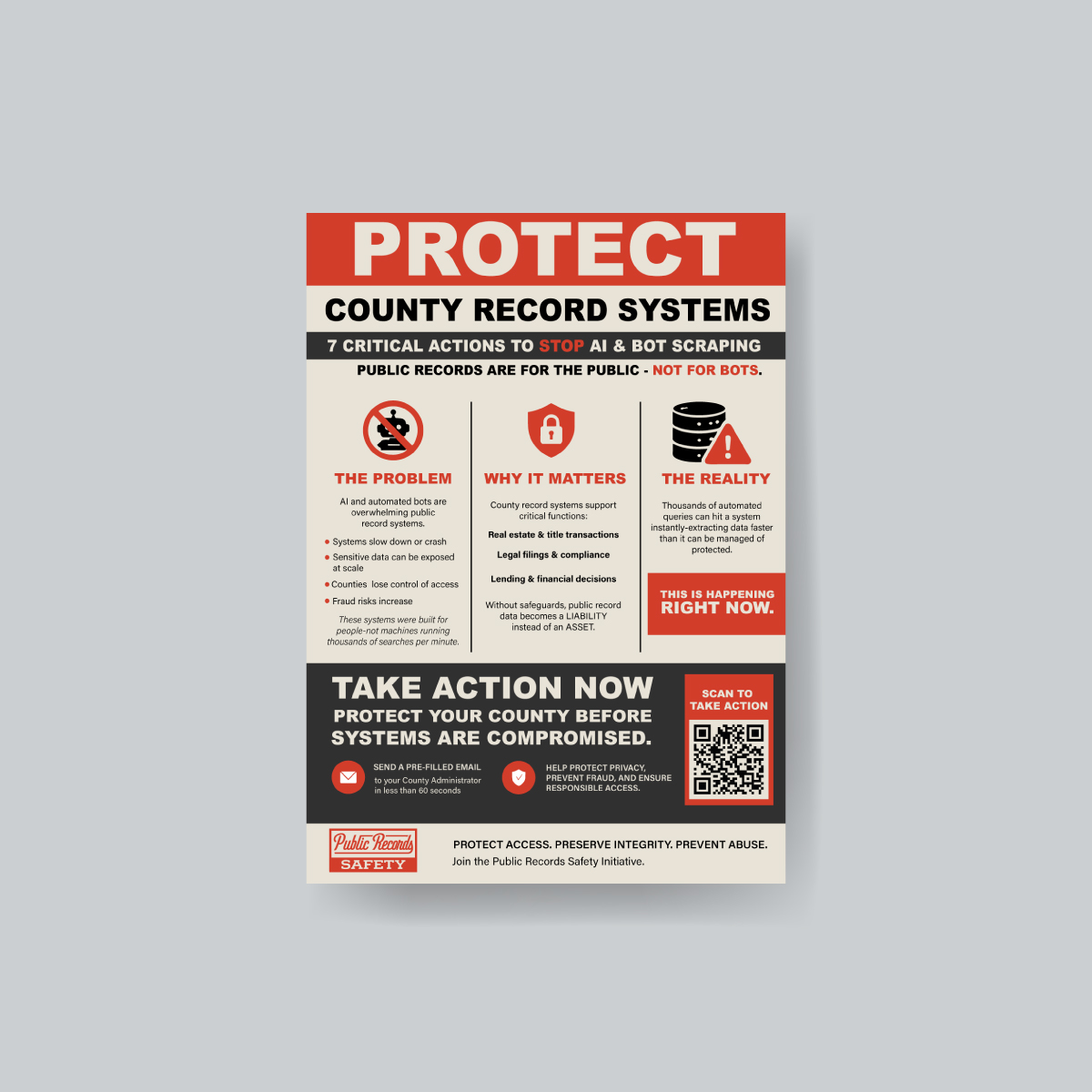
Public Records Safety has created a printable awareness flyer designed for county clerks, recorders, IT administrators, assessors, and public records departments. This resource explains the growing risks tied to uncontrolled bot scraping, mass data harvesting, privacy exposure, and operational strain on county record systems.
The flyer is designed to help vendors, abstractors, title professionals, and concerned stakeholders start productive conversations with local government offices about responsible public record access and stronger portal protections.
Understand how automated access is affecting your system.
Evaluate your current exposure and vulnerabilities.
Apply basic protections and policy controls.
Work with vendors, abstractors, and stakeholders.
Adapt as technology and threats evolve.
Enter a county name to check its protection status